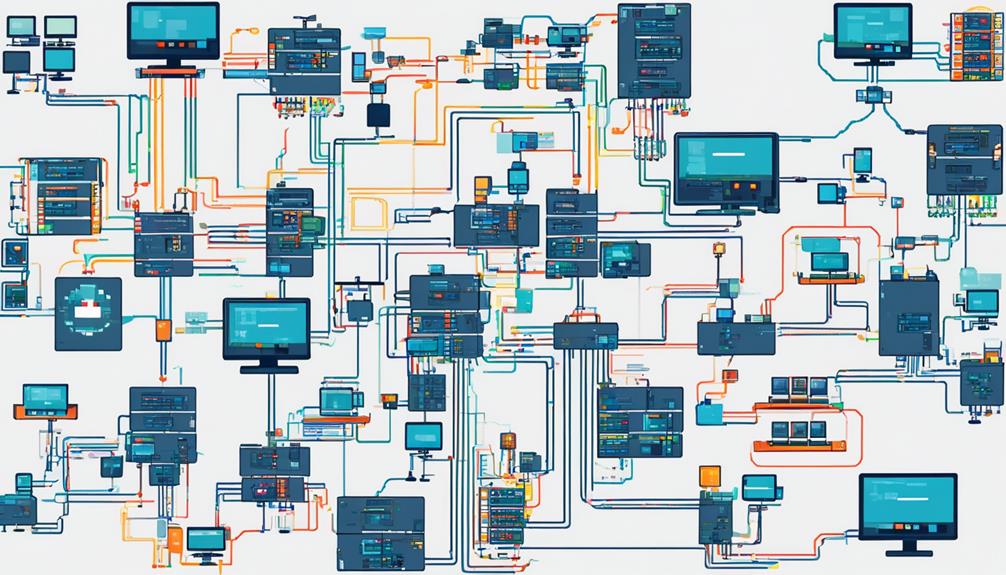
Network infrastructure optimization techniques play a crucial role in ensuring the smooth operation and efficiency of modern networks. With the increasing reliance on technology and digital connectivity, organizations are constantly seeking ways to enhance their network performance.
By assessing network requirements, implementing traffic analysis, and optimizing network infrastructure, organizations can unlock the full potential of their network infrastructure. Utilizing bandwidth management techniques, ensuring network security, and configuring network protocols for performance are also important strategies for achieving optimal network performance and efficiency.
In this discussion, we will explore these techniques in detail, shedding light on their benefits and providing insights into how organizations can improve their network infrastructure to achieve optimal performance and efficiency.
Key Takeaways
- Thorough evaluation of organization's objectives, growth plans, user base, device usage, and application needs is essential for network performance optimization.
- Optimization of network infrastructure and utilization of traffic analysis tools can help identify and resolve bottlenecks and congestion areas.
- Implementation of Quality of Service (QoS) and network management systems can help allocate and prioritize network resources for improved performance.
- Continual network monitoring, maintenance, and regular hardware and software updates are crucial for ensuring optimal network performance and security.
Assessing Network Requirements
Assessing network requirements involves a thorough evaluation of the organization's objectives, growth plans, user base, device usage, application needs, and data traffic patterns to design a scalable and secure network infrastructure. This process is crucial for ensuring optimal network performance, bandwidth utilization, and overall efficiency.
To assess network requirements, it is essential to understand the organization's objectives and growth plans. This includes determining the expected number of users and devices that will utilize the network. By identifying these factors, organizations can accurately estimate the required network capacity and plan for future expansions.
Another important aspect of assessing network requirements is evaluating the application needs. Different applications may have varying bandwidth requirements, and understanding these requirements is essential for optimizing network performance. By analyzing application data traffic patterns, organizations can allocate the necessary bandwidth to ensure smooth and uninterrupted application usage.
Monitoring network performance is also crucial when assessing network requirements. This involves using software and hardware tools to collect and analyze network metrics such as latency, packet loss, and throughput. By monitoring these metrics, organizations can identify potential bottlenecks and areas for optimization.
Optimization is a key component of network requirements assessment. It involves fine-tuning the network infrastructure to improve performance, reduce latency, and enhance overall user experience. This may involve implementing quality of service (QoS) policies, upgrading hardware components, or optimizing network protocols.
Effective network management is another consideration when assessing network requirements. This includes implementing network management systems that provide visibility and control over the network infrastructure. By having centralized management capabilities, organizations can efficiently monitor and troubleshoot network issues, ensuring smooth network operations.
Implementing Traffic Analysis
To enhance network visibility and optimize traffic flow, the implementation of traffic analysis is crucial in ensuring efficient prioritization of bandwidth-intensive applications. Traffic analysis involves the examination of data packets flowing through a network to identify and understand patterns, trends, and potential issues. By analyzing traffic, organizations can gain insights into the behavior of applications and users, enabling them to optimize network performance and improve the overall user experience.
The following are three key benefits of implementing traffic analysis:
- Optimizing Network Performance:
Traffic analysis allows organizations to identify and prioritize bandwidth-intensive applications, ensuring that mission-critical applications receive the necessary resources. By understanding the traffic patterns and demands, network administrators can allocate resources effectively, preventing congestion and bottlenecks.
- Identifying and Managing Applications:
Traffic analysis helps organizations identify the applications consuming the most bandwidth. By understanding which applications are most critical, organizations can allocate resources accordingly and implement quality of service (QoS) techniques to prioritize network traffic.
- Enhancing Security:
Traffic analysis can also be instrumental in identifying potential security threats. By monitoring traffic patterns and analyzing packet data, network administrators can detect anomalies and potential attacks. This proactive approach to network defense allows organizations to mitigate risks and prevent potential breaches.
To implement traffic analysis effectively, organizations can leverage network optimization tools and solutions like Kentik's Network Observability Cloud. These tools provide real-time visibility into bandwidth-intensive applications, allowing administrators to monitor and analyze traffic patterns, optimize network performance, and ensure the efficient allocation of resources.
Optimizing Network Infrastructure
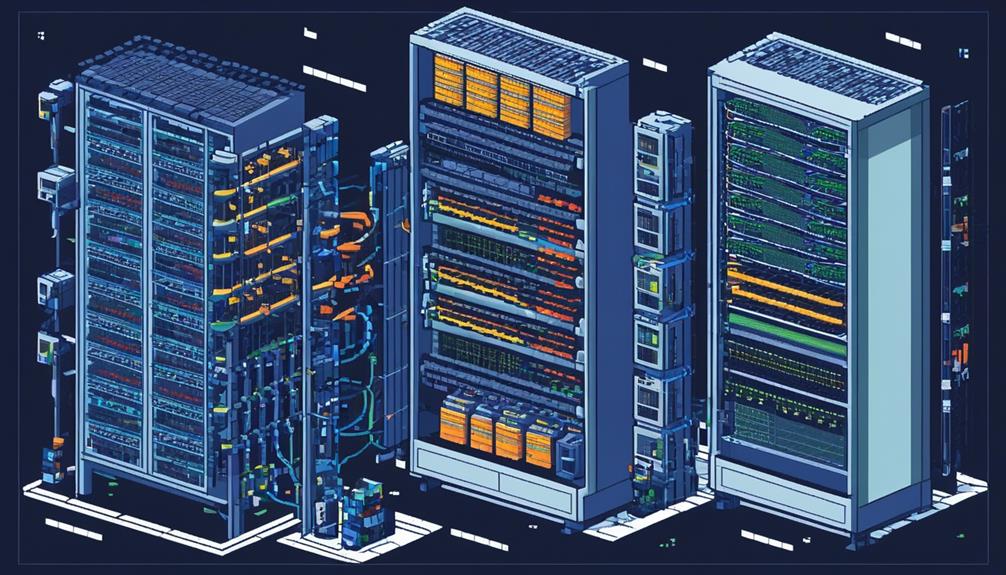
Optimizing network infrastructure is crucial for achieving performance enhancements and cost reduction.
By carefully selecting and configuring network hardware, organizations can ensure efficient utilization of resources and improve network performance.
Implementing effective bandwidth management techniques, such as throttling and traffic shaping, further enhances network optimization by prioritizing critical applications and preventing congestion.
Additionally, robust network security measures, including DDoS protection and encryption, play a vital role in optimizing network infrastructure by safeguarding against potential threats and maintaining uninterrupted operations.
Performance Enhancements
By leveraging traffic analysis and strategic prioritization, performance enhancements can be achieved in optimizing the network infrastructure. To achieve this, network administrators can implement the following network infrastructure optimization techniques:
- Utilize traffic analysis tools to gain insights into network traffic patterns and identify bottlenecks or areas of congestion. This information can then be used to optimize traffic flow and prioritize mission-critical applications.
- Carefully select, configure, and update network hardware to ensure optimal performance. This includes choosing switches, routers, and other network devices that meet the organization's requirements and regularly updating firmware and software to take advantage of new features and bug fixes.
- Implement bandwidth management techniques such as Quality of Service (QoS) to efficiently allocate and prioritize network resources. This allows for the prioritization of critical applications and ensures that bandwidth is allocated according to business needs.
Cost Reduction
One effective approach to achieving cost reduction in network infrastructure optimization is through the implementation of efficient resource allocation and utilization strategies. By leveraging network monitoring tools and Network Performance Monitoring software, organizations can gain insights into network performance metrics such as packet loss, bandwidth usage, and Quality of Service (QoS). This allows for the identification of areas for improvement and optimization. Additionally, optimizing network bandwidth through techniques like traffic shaping enables targeted allocation of bandwidth for business-critical operations, reducing the need for costly network upgrades. Furthermore, careful selection and configuration of network hardware, along with modular designs for resilience and scalability, can minimize the need for frequent hardware replacements and upgrades, resulting in long-term cost savings. The following table provides a summary of cost reduction techniques in network infrastructure optimization:
| Cost Reduction Techniques |
|---|
| Efficient resource allocation and utilization strategies |
| Leveraging network monitoring tools and Network Performance Monitoring software |
| Optimization of network bandwidth through traffic shaping |
| Careful selection and configuration of network hardware |
| Implementation of modular designs for resilience and scalability |
Utilizing Bandwidth Management Techniques
Bandwidth management techniques play a crucial role in optimizing network resources and ensuring efficient data transmission. By effectively managing the network capacity and prioritizing network traffic, organizations can maintain high-performance connectivity.
Here are three key subtopics related to utilizing bandwidth management techniques:
- Load Balancing: Load balancing is an essential aspect of network optimization strategies. It involves distributing network traffic evenly across multiple network connections or servers. By evenly distributing the load, organizations can prevent bottlenecks and ensure that network resources are utilized efficiently. Load balancing can be achieved through various methods, such as round-robin, least connections, or weighted algorithms.
- Traffic Prioritization: Prioritizing network traffic is crucial for business-critical operations. By allocating targeted bandwidth to applications and services that require high-performance connectivity, organizations can ensure smoother operations. Traffic shaping and quality of service (QoS) techniques can be employed to prioritize certain types of traffic over others, based on predefined rules. This allows critical applications to receive the necessary bandwidth, minimizing the impact of less important traffic.
- Monitoring and Analysis: To effectively utilize bandwidth management techniques, organizations must monitor and analyze their network traffic patterns. By monitoring network performance and traffic utilization, organizations can identify bottlenecks, bandwidth-intensive applications, and potential areas for improvement. This information can then be used to fine-tune bandwidth allocation, adjust load balancing configurations, and optimize network resources accordingly.
Ensuring Network Security

To safeguard network infrastructure from potential threats and vulnerabilities, organizations must prioritize network security measures and regularly update protocols and security measures. Network security is crucial for maintaining the overall network performance and protecting the organization's sensitive data and resources.
There are several network infrastructure optimization techniques that network admins can employ to ensure network security.
One important aspect of network security is implementing robust security measures such as DDoS detection and protection, firewalls, intrusion detection systems, and encryption. These measures help prevent unauthorized access, detect and mitigate attacks, and encrypt sensitive data to ensure its confidentiality and integrity.
In addition to these security measures, organizations should also prioritize network traffic that supports business-critical operations. This can be achieved by allocating targeted bandwidth to critical applications and services, ensuring their smooth operation and minimizing the impact of potential security threats on their performance.
Configuring network protocols is another important aspect of network security optimization. By optimizing protocols, network admins can enhance network speed and reliability, reducing the chances of performance issues and vulnerabilities. Additionally, considering migration to IPv6 can provide improved addressing capabilities and built-in security features.
To ensure continuous network security, organizations should regularly monitor network performance and conduct routine maintenance. This includes updating hardware and software, upgrading firmware, and performing regular health checks to identify and address any potential vulnerabilities or performance issues promptly.
Configuring Network Protocols for Performance
As network security measures are crucial for safeguarding the organization's sensitive data and resources, the configuration of network protocols plays an integral role in enhancing network performance and ensuring seamless connectivity. Configuring network protocols involves adjusting settings in TCP/IP to enhance speed and reliability, understanding traffic characteristics, and considering migration to IPv6 for improved addressing and security features.
To optimize network protocols for performance, several techniques can be employed:
- Traffic shaping: By prioritizing certain types of network traffic over others, traffic shaping can improve the overall performance of the network. This technique involves setting limits on the bandwidth allocated to different applications or users, ensuring that critical traffic gets priority.
- Quality of Service (QoS): QoS settings allow network administrators to allocate network resources based on the type of traffic. By assigning different levels of priority to various types of data, such as voice or video, QoS ensures that critical applications receive the necessary bandwidth and resources for optimal performance.
- Protocol optimization: Network protocols can be optimized to minimize latency, packet loss, and jitter. This involves adjusting parameters such as window sizes, congestion control algorithms, and buffer sizes to improve the efficiency of data transmission.
Proper configuration of network protocols is essential for supporting data-intensive applications and ensuring uninterrupted access to resources and services. By minimizing latency, packet loss, and jitter, network protocol configuration improves real-time data transfer, making it ideal for applications that require instant response, such as video conferencing or online gaming.
Continual Network Monitoring and Maintenance

Continual network monitoring and maintenance are essential for ensuring optimal performance and proactively addressing any potential issues that may arise. By implementing best practices used in network monitoring and maintenance, organizations can effectively improve network performance and create an efficient network infrastructure.
There are several practices used to monitor and maintain a network, including regular hardware and software updates, firmware upgrades, and routine network health checks. These measures help ensure that critical components are up to date and functioning properly, minimizing the risk of performance degradation.
To enhance network performance, organizations should prioritize network traffic based on its importance. This can be achieved by implementing Quality of Service (QoS) policies that prioritize critical traffic, such as real-time communication or business-critical applications, over less important traffic. By prioritizing network traffic, organizations can ensure that essential services are always given the necessary bandwidth and resources to function optimally.
Another important aspect of continual network monitoring and maintenance is the ability to measure a series of key performance indicators (KPIs). This process is used to assess the overall health of the network and identify any potential bottlenecks or areas for improvement. By regularly measuring KPIs such as network latency, packet loss, and throughput, organizations can identify performance issues and make the necessary changes to remove bottlenecks and optimize network performance.
The benefits of network monitoring and maintenance extend beyond just performance improvements. By continually monitoring the network, organizations can proactively identify security vulnerabilities and take the necessary steps to mitigate them. Additionally, ongoing maintenance helps organizations identify aging or faulty equipment that may require replacement, reducing the risk of unexpected downtime.
Frequently Asked Questions
How Do You Optimize Network Infrastructure?
To optimize network infrastructure, several techniques can be employed.
Bandwidth allocation ensures that resources are efficiently distributed to support business-critical operations and avoid congestion.
Traffic analysis helps identify network bottlenecks and prioritize mission-critical applications.
Network monitoring ensures ongoing performance assessment and troubleshooting.
Quality of Service (QoS) techniques enable packet prioritization and latency reduction.
Network virtualization and segmentation enhance scalability and security.
Load balancing distributes traffic evenly across multiple servers.
Lastly, implementing robust security measures, such as encryption and DDoS detection, further optimize the network infrastructure.
What Is Network Optimization Technique?
Network optimization techniques are strategies and practices used to improve the performance and efficiency of a network. This involves analyzing network data and metrics to identify areas for improvement, implementing traffic analysis, optimizing network infrastructure, managing bandwidth, ensuring network security, and configuring network protocols.
Data analysis plays a crucial role in network optimization, providing insights into network performance and helping to identify bottlenecks. Best practices include ongoing monitoring, maintenance, and troubleshooting.
Successful case studies demonstrate the benefits of network optimization, such as improved performance, reduced downtime, cost savings, enhanced security, and improved user experience.
What Are Network Models in Optimization Techniques?
Network models in optimization techniques are mathematical and computational algorithms used to simulate and optimize network behavior. They play a crucial role in guiding strategic changes and resource allocation for various industries.
In business, network models help in optimizing resource allocation in manufacturing processes. In transportation, they aid in efficient routing and optimizing energy distribution systems. Network models also find applications in supply chain management, healthcare systems, urban planning, disaster management, and telecommunications, providing advantages such as identifying bottlenecks and improving network performance.
However, implementing network models in these domains can present challenges.
How Do I Optimize My Network Connection?
To optimize a network connection, several techniques can be employed.
These include:
- Bandwidth management
- Latency reduction
- Traffic prioritization
- Implementation of Quality of Service (QoS)
- Network caching
- Load balancing
- Network segmentation
- Packet inspection
- Utilization of network monitoring tools
- Wireless network optimization